Features
Making sense of ones and zeroes
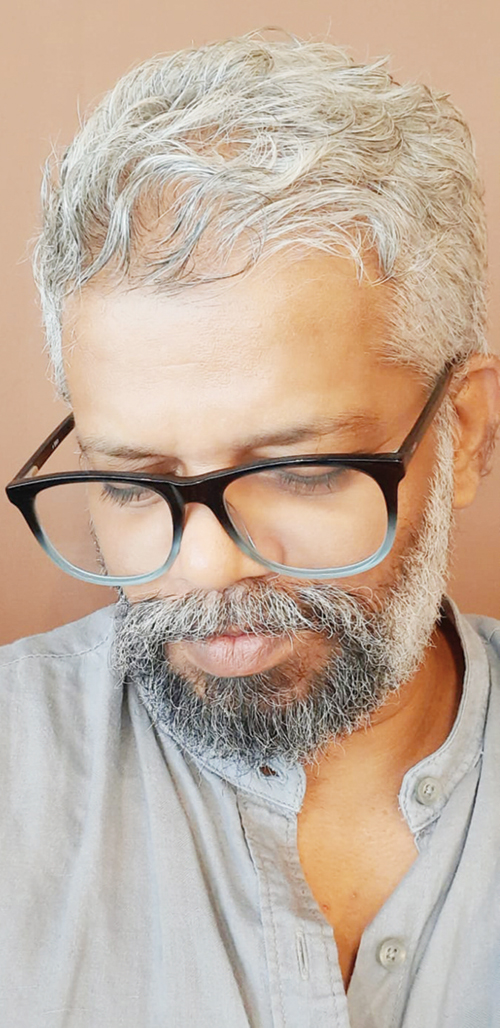
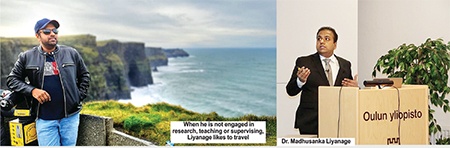
Dr. Madhusanka Liyanage: First Sri Lankan to win IEEE Outstanding Young Researcher Award
By Sajitha Prematunge
Oblivious to the laws of physics and before he could even grasp the meaning of the word velocity, he tried to calculate the speed of the bus he was travelling in, by taking into account how long it took the bus to travel between two lamp posts. He was just seven years old then. By grade three he was trying to calculate the light year longhand. It’s not rocket science, it was just a matter of multiplying how far light travelled in a second, by how many seconds there are in a year. But for an eight-year-old to even entertain such an idea, while his peers were still playing cops and robbers, is uncanny.
In any other country he would have been celebrated as a math prodigy. So it came as no surprise when, this year, Dr. Madhusanka Liyanage won the Outstanding Young Researcher Award presented by the Communications Society of Institute of Electrical and Electronics Engineers, one of the biggest engineering societies in the world. The award is presented to the 2nd Best Young Researcher in the region, in Liyanage’s case it is Region 8, which included Europe, the Middle East and Africa.
Award
Research performance of candidates was a major criteria for the Outstanding Young Researcher Award. The number of academic papers published in journals and conference papers produced in the last three years, for example, were graded depending on the ‘impact factor’ of the publication or conference, with contributions to IEEE journals and conferences receiving extra credit. Citations of work in the past three years is also considered, as well as contribution to the society in the form of the number of conferences or workshops organised and journals edited. Positions held within the IEEE society is given special consideration and Liyanage was elevated to the position of senior member this year. “It’s not just my award, my team of students, mentors and anyone else who had helped me throughout my career all played a vital role in my success.”
 Born in Udugama, Galle, in 1985 Liyanage is the youngest in a family of three.”Everyone else in the family have a knack for business.” Both his elder brother and sister took after their businessman father, Sunil Ranjith Liyanage. The youngest Liyanage took after his mother, Magalika Hegodaarchthi. When asked whether his mathematics teacher-mother was influential in his academic trajectory, Liyanage readily admitted that she was a positive influence. He was exposed to math at an early age. His mother still fondly reminisces how the six-year-old parked himself at the back row of her math tuition class trying to solve problems meant for 14-year-olds. “Perhaps the exposure motivated me,” said Liyanage. “Math was the only subject that made sense to me. In fact, I am not good at any other subject.” His uncle bought him the book, ‘How to become an engineer’ when he was still in grade three, the math problems in which he avidly devoured. “In fact, I can’t remember a time I wanted to be anything other than an engineer,” chuckled Liyanage.
Born in Udugama, Galle, in 1985 Liyanage is the youngest in a family of three.”Everyone else in the family have a knack for business.” Both his elder brother and sister took after their businessman father, Sunil Ranjith Liyanage. The youngest Liyanage took after his mother, Magalika Hegodaarchthi. When asked whether his mathematics teacher-mother was influential in his academic trajectory, Liyanage readily admitted that she was a positive influence. He was exposed to math at an early age. His mother still fondly reminisces how the six-year-old parked himself at the back row of her math tuition class trying to solve problems meant for 14-year-olds. “Perhaps the exposure motivated me,” said Liyanage. “Math was the only subject that made sense to me. In fact, I am not good at any other subject.” His uncle bought him the book, ‘How to become an engineer’ when he was still in grade three, the math problems in which he avidly devoured. “In fact, I can’t remember a time I wanted to be anything other than an engineer,” chuckled Liyanage.
Education
Liyanage received his primary education in Udugama Maha Vidyalaya. The grade five scholarship examination results qualified him to enrol in Richmond College, Galle and A/Ls got him through to the Moratuwa University, where he obtained his B.Sc. Degree, with First Class Honours, in electronics and telecommunication engineering, in 2009. “3G was just rolling out and it was an exciting time to be in the telecommunications field,” said Liyanage. He received a scholarship to Asian Institute of Technology, even before he completed his bachelors. He completed his Master in Engineering (M.Eng.) from the Asian Institute of Technology, Bangkok, Thailand, in 2011. After a year at AIT he moved to France on a dual degree programme, where he obtained a Master of Science (M.Sc.) from the University of Nice Sophia Antipolis, France.
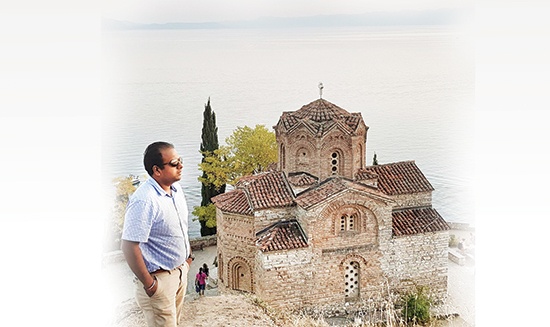
In 2004, right after his A/Ls he represented Sri Lanka in the 45th International Mathematical Olympiad, held in Europe. Since that first taste of Europe, he had been drawn to it and knew then that one day he would make it his second home. In Finland, considered the base of telecommunication with big-name companies like Nokia and Huawei setting up shop there, Liyanage obtained a PhD in communication engineering from the University of Oulu, in 2016.
Then his path diverged. “I could opt for a job in the industry or stay in the academic track.” He decided to remain an academic. Between 2015 and 2018 he functioned as a visiting Research Fellow at various institutions such as Data61, CSIRO, Sydney, Australia, the data and digital specialist arm of Australia’s national science agency; Infolabs21, Lancaster University, UK; School of Computer Science and Engineering, University of New South Wales; School of IT, University of Sydney and computer science laboratory LIP6, Sorbonne University.
In 2018, he received the Docentship from the University of Oulu, Finland, within 18 months from the PhD, making Liyanage the only researcher to receive the Docentship so soon. He worked as an adjunct professor at the University of Oulu while engaged in his post doctoral studies. He joined the School of Computer Science, University College Dublin (UCD), Ireland, early this year as an assistant professor and Ad Astra Fellow with the prestigious Marie Skłodowska-Curie Actions Individual Fellowship. The fellowship is one of highly reputed fellowships offered by the European Union.
Research
Liyanage’s main research interest is telecommunication network, 5G and 6G mobile networks in particular, focusing on network security concerns. “The major change we can expect with the transfer from 4G to 5G will be the number of devices that will be connected to the system.” He explained that although we only connect mobile devices such as mobile phones, tabs and laptops to the network, the advent of 5G will allow more devices, such as smart wearables, to be connected to the network. 6G will further expand the horizon to include the whole shebang, or Internet of things (IoT). In lay terms IoT is the network of physical objects, referred to here by ‘things’, that exchange data with other devices and systems over the Internet.
“These new devises don’t have the standard security measures that mobile devises and laptops have, making them more susceptible to cyber attacks.” Liyanage explained that there are only a handful of mobile device manufacturers in the world, consequently all mobile devices have in place stringent security control measures and are required to follow strict standards. “There is a large number of IoT device manufacturers, and are not bound to follow such strict security measures.” Liyanage explained that such devices are susceptible to cyber attacks and can, in fact, be used as entry points for attacks on the 5G network. “Besides some IoT devices are considerably smaller and, therefore, does not have a lot of processing power. Consequently, they cannot support high power security mechanisms.”
Liyanage further explained that even reputed manufacturers of IoT devices, opt out security tests, due to related costs and time constraints imposed by high competition. “A major drawback in 5G is that it is a software controllable network and software based systems are generally more vulnerable than hardware based systems.” He elaborated that 5G is an open architecture platform, which will enable software developers to understand, and possibly manipulate it.
What has the potential to make matters worse is that, after all IoT devices are interconnected, the next step will be to integrate all critical infrastructure such as the power grid, transportation network or water managements systems. “These can be monitored by IoT devices via 5G.” Liyanage pointed out a major security risk arguing that any terrorist or cyber criminal with a decent IoT device could hack into such systems and thereby wreak havoc with any of the aforementioned critical infrastructure.
He explained that 6G will enable the integration of Artificial Intelligence into the system. “It will be a mostly automated, self sustaining network, centrally controlled by an AI. “AI is essentially a good thing as long as it is used for the good,” said Liyanage. But it can also be manipulated to achieve malicious ends, according to him. “For example, if someone creates a malicious intelligent agent, it can identify loopholes in the system and self perform attacks on it.” The sci-fi like evil AI agent stuff may come off like an episode of ‘Person of Interest’, but Liyanage maintains it is entirely plausible. Consequently, he reiterated the requirement of straightening out the AI related security issues before considering launching the 6G system. “We have to consider everything from the data fed to the AI to what kind of effect it will have on the AI and how reliable the AI algorithm will be.”
All these maybe years away and will no doubt have repercussions of global relevance. But what are the more immediate threats at individual level when switching to 5G? “It will have a huge impact on society. So far we only connect mobiles, tabs and laptops to the system.” But with a full-fledged 5G system, expected sometime between 2025 to 2030, a lot more IoT devices will be interconnected via the system. “These devices can collect a lot of personal information. For example, from cameras on mobile phones to smart TVs, every new device comes with a built in camera. It won’t be long before many strap smart wearable that store health information.” Liyanage pointed out that this wealth of personal information, most of which is uploaded on to cloud services, can easily be stolen. “This is a major violation of privacy.” He emphasised that, at an age when everyone in society is connected to the system most of the time by at least one device such as the mobile phone a proper privacy protection mechanism should be put in place to counter such privacy violations.
When asked whether 5G or 6G posed renewed individual financial security threats, Liyanage pointed out that such information is already available on most devices connected to the 4G system. “But they are connected through personal Wi-Fi, which is safe as long as you maintain it password protected.”
Blockchain applications, another research area that appeals to Liyanage, may just provide the solution for a host of these security issues. For those uninitiated in telecommunication networking, Blockchain applications are cryptography used to secure transactions made using cryptocurrency. Blockchain technology became popular a decade ago and gained momentum because of Bitcoin cryptocurrency, the digital equivalent of money. It may be just a bunch of ones and zeroes but daily transactions using cryptocurrency can amount to billions.
“Bitcoin cryptocurrency is a beautiful innovation but what’s more interesting is the technology used to secure transactions made using cryptocurrency, blockchain, because of its applications in other areas such as telecommunication.” Liyanage pointed out that some of the pressing security issues of 5G and 6G can be solved using blockchain technology. “The biggest advantage of Bitcoin cryptocurrency is that it eliminates the third party. For example, if two people want to make a transaction, it has to be done through the bank. But with Bitcoin, transactions can be made direct.”
So, what are its implications for telecommunication? “The same concept can be used in telecommunication,” explained Liyanage. “There are certain instances where a third party is required. Roaming is a case in point.” Roaming allows the use of a mobile connection while outside the range of its home network by connecting to another available network in the country of travel. “To achieve this, the home country service provider should have an existing agreement with the visiting country operator.” When two parties who do not know each other want to enter into an agreement, in order to ensure that both parties keep their end of the bargain, a trusted neutral third party must intervene, and be paid for, for their pains. Blockchain can offer this trust and is far more preferable to a physical third party as is requires no commission. “Anywhere a third party is required, they can be replaced by a blockchain.”
There are many other such applications, according to Liyanage. “It can be used in service-level or SLA agreements. For example, if a user enters into an agreement with a telecommunications service provider, on his or her own terms, a third party must ensure that both parties keep to their agreement.”
Multitasker
Liyanage currently supervises nine PhD students and three Master students in four different universities. He is also a visiting Lecturer at Moratuwa University, Sri Jayewardenepura University and Yangon Technological University, Myanmar. In addition to conducting lectures for Undergraduate and master courses at the University College Dublin, supervising postgraduate students, mentoring postdoctoral researchers and functioning as the principle investigator for various national and internal research projects, Liyanage has found time to publish over 100 research articles and three books. When asked how he achieve all this at such a young age, with two masters and a PhD to boot, Liyanage attributes it to his time management skills.
“I may not always have my nose in a book, but I manage my time efficiently.” He takes after his parents, who happen to be early birds, waking up at 4 am. From four to eight or nine he dedicates to research work. “Having the satisfaction that I have done my job for the day, I can fool around all I want the remaining 10 hours or so. I think life needs this kind of balance.”
Unlike Sri Lankan students, who are forced to work in the government or corporate sector while reading for a master or PhD, Liyanage didn’t have to sacrifice valuable time on a job unrelated to his field of work. Liyanage was paid to do research and this, he points out is the fundamental difference between European countries and Sri Lanka. “I hardly know any full-time PhD students in Sri Lanka. Most of them are forced to lecture. PhDs require dedication.” He admitted that his academic load of University College Dublin is comparatively low allowing him to dedicate more time to research. Usually a lecturer is required to teach three modules per year, but because he is an Ad Astra Fellow, he is required to teach only one module. “In a bid to encourage research, University College Dublin hired 100 lecturers over a four-year period as Ad Astra Fellows, who would have limited academic load.”
It’s quite the opposite in Sri Lanka, pointed out Liyanage. “There are talented students and lecturers in Sri Lanka, but they are overloaded. Some lecturers are required to teach three modules in a single semester.” He also pointed out the lack of research funding and grants. “It should come from either the government of the corporate sector. To attract good PhD students remuneration equivalent to industry sector salaries must be offered.”
Liyanage’s achievements are not solely academic. The multitasker also has a patent to his credit. During a short stint at General Electronics, their branch in Italy wanted to replace the wired communication mechanism between the head and the tail of trains built by them, with wireless communication. “Because wired connections were a hassle when changing carriages. But wireless communication mechanisms are relatively less secure, because open air transmissions can be intercepted.” Liyanage built a secure wireless communication mechanism, which was patented. When he is not engaged in research, teaching or supervising, Liyanage likes to travel.
Features
The Ramadan War

A Strategic Assessment of a Conflict Still Unresolved
The Unites States of America and its ally, Israel attacked Iran on 28 February, or the 10th day of the month of Ramadan. More than a month of intense fighting has passed since, and the Ramadan War has settled into a grinding, attritional struggle that defies early declarations of victory. Despite sustained U.S. and Israeli air and naval bombardment, Iran remains standing, and continues to strike back with a level of resilience that has surprised many observers. The conflict has evolved into a contest of endurance, adaptation, and strategic innovation, with each side attempting to impose costs the other cannot bear.
Iran’s response to the overwhelming airpower of its adversaries has been both simple and devastatingly effective: saturate enemy defences with swarms of inexpensive drones and older ballistic missiles, forcing them to expend costly interceptors and reveal radar positions, and then follow up with salvos of its most advanced precisionguided missiles. This layered approach has inflicted severe physical damage on Israel and has shaken its national morale. The country has endured repeated missile barrages from Iran and rocket fire from Hezbollah, straining its airdefence network and pushing its civilian population to the limits of endurance.
The United States, meanwhile, has been forced to evacuate or reduce operations at several bases in the Gulf region due to persistent Iranian drone and missile attacks. For both the U.S. and Israel, the war has become a test of strategic credibility. For Iran, by contrast, victory is defined not by territorial gains or decisive battlefield outcomes, but by survival, and by continuing to impose costs on its adversaries.
The central strategic objective for the U.S. has now crystallised: reopening the Strait of Hormuz to secure global energy flows. Ironically, the Strait was open before the war began; it is the conflict itself that has rendered it effectively closed. Air and naval power alone cannot achieve this objective. The geography of the Strait, combined with Iran’s layered defences, means that any lasting solution will require ground forces, a reality that carries enormous risks.
U.S. Strategic Options
The United States faces five broad operational options, each with significant drawbacks.
1. Seizing Kharg Island
Kharg Island handles roughly 90% of Iran’s oil exports, making it an attractive target. However, it lies only a short distance from the Iranian mainland, where entrenched Iranian forces maintain dense networks of missile batteries, drones, artillery, and coastal defences. Any attempt to seize Kharg would require first neutralising or capturing the adjacent coastline, a costly amphibious and ground operation.
Even if successful, this would not reopen the Strait of Hormuz. It would merely deprive Iran of export capacity, which is not the primary U.S. objective. At least ostensibly not; there are those who argue that the U.S. simply wants to take over Iran’s petroleum (see below).
2. Forcing the Strait of Hormuz by Naval Power
Sending U.S. naval forces directly through the Strait is theoretically possible but operationally hazardous. Iran has mined all but a narrow channel hugging its own shoreline. That channel is covered by overlapping fields of antiship missiles, drones, artillery, and coastal radar. Clearing the mines would require prolonged operations under fire. Attempting to push through without clearing them would risk catastrophic losses.
3. Capturing Qeshm, Hengam, Larak, and Hormuz Islands
These islands dominate the Iranian side of the Strait and host radar, missile, and drone installations. Capturing them would degrade Iran’s ability to close the Strait, but the islands are heavily fortified, and the surrounding waters are mined. Amphibious assaults against defended islands are among the most difficult military operations. Even success would not guarantee the Strait’s longterm security unless the mainland launch sites were also neutralised.
4. Invading Southern Iraq and Crossing into Khuzestan
This option would involve U.S. forces advancing through southern Iraq, crossing the Shatt alArab waterway, and pushing into Iran’s Khuzestan province — home to most of Iran’s oilfields. The terrain is difficult: marshes, waterways, and narrow approaches. Iranian forces occupy the high ground overlooking the plains.
While this route would allow Saudi armoured forces to participate, it would also expose U.S. and allied logistics to attacks by Iraqi Shia militias, who have already demonstrated their willingness to target U.S. assets. The political and operational risks are immense.
5. Capturing Chabahar and Advancing Along the Coast
The most strategically promising — though still costly — option is seizing the port of Chabahar in southeastern Iran and advancing roughly 660 kilometres along the coast toward Bandar Abbas. This approach offers several advantages:
· Distance from Iran’s core population centres complicates Iranian logistics.
· Chabahar’s deepwater port (16m draught)
would provide a valuable logistics hub.
· U.S. carriers could remain at safer standoff distances
, supporting operations without entering the Strait.
· The coastal route allows naval gunfire and missile support
to assist advancing ground forces.
· Local Baluchi insurgents
could provide intelligence and limited support.
· Capturing Bandar Abbas would
outflank Iran’s island defences and effectively reopen the Strait.
This option is likely to form the backbone of any U.S. ground campaign, potentially supplemented by diversionary attacks by regional partners to stretch Iranian defences.
The Limits of U.S. Superiority
The United States retains overwhelming superiority in naval power and manned airpower. But whether this advantage translates into dominance in unmanned systems or ground combat is far from certain.
The 2003 invasion of Iraq is often cited as a model of U.S. military prowess, but the comparison is misleading. Iraq in 2003 had been crippled by a decade of sanctions. Its forces lacked modern mines, antitank missiles, and effective air defences. Tank crews had little training; some could not hit targets at pointblank range. RPG teams were similarly unprepared. The U.S. enjoyed numerical superiority in the theatre and total control of the air, allowing it to isolate Iraqi units and prevent reinforcement.
Even under those favourable conditions, Iraqi forces managed to delay the U.S. advance. At one point, forward U.S. units nearly ran out of ammunition and supplies, forcing the diversion of forces intended for the assault on Baghdad to secure the lines of communication.
Iran is not Iraq in 2003. Its armed forces and industrial base have adapted to nearly half a century of sanctions. It produces its own drones, missiles, artillery, and armoured vehicles. It has built extensive underground facilities, hardened command posts, and redundant communication networks.
Moreover, the battlefield itself has changed. The RussoUkrainian war demonstrated that deep armoured penetrations – once the hallmark of U.S. doctrine – are now extremely vulnerable to drones, loitering munitions, and precision artillery. The result has been a return to attritional warfare reminiscent of the First World War, with front lines stabilising into trench networks.
Yet, as in the First World War, stalemate has been broken not by massed assaults but by small, highly trained teams infiltrating thinly held lines, identifying targets, and guiding drones and artillery onto enemy positions deep in the rear. Iran has studied these lessons closely.
Mosaic Defence and Transformational Warfare
Iran’s military doctrine has evolved significantly over the past two decades. Its “mosaic defence” decentralises command and control, ensuring that even if senior leadership is targeted, local units can continue operating autonomously. This structure proved resilient during the initial waves of U.S. and Israeli strikes.
Iran has also absorbed lessons from U.S. “shock and awe” operations. The botched U.S. invasion of Grenada in 1983 exposed weaknesses in joint operations, prompting the development of “effectsbased operations,” “rapid dominance” and the broader concept of “transformational warfare.” These doctrines (better known colloquially as “Shock and Awe”), influenced by Liddell Hart and Sun Tzu, emphasised simultaneous strikes on strategic targets to paralyse the enemy’s decisionmaking.
While the U.S. struggled to apply these concepts effectively in Iraq and Iran, Tehran has adapted them for asymmetric use. Its drone and missile campaigns have targeted not only military assets but also economic infrastructure and psychological resilience. Israel’s economy and morale have been severely tested, and the United States finds itself entangled in a conflict that offers no easy exit.
Iran has also pursued a broader strategic objective: undermining the petrodollar system that underpins U.S. financial dominance. By disrupting energy flows and encouraging alternative trading mechanisms, Iran seeks to weaken the economic foundations of U.S. power.
Will the USA Achieve Its War Aims?
The United States’ core objective appears to be securing control over global energy flows by reopening the Strait of Hormuz and limiting China’s access to Middle Eastern oil before it can transition to alternative energy sources. Whether this objective is achievable remains uncertain.
A ground campaign would be long, costly, and politically fraught. Iran’s defences are deep, layered, and adaptive. Its drone and missile capabilities have already demonstrated their ability to impose significant costs on technologically superior adversaries. Regional allies are cautious, and global support for a prolonged conflict is limited.
The United States retains overwhelming military power, but power alone does not guarantee strategic success. Iran’s strategy is simple: survive, adapt, and continue imposing costs. In asymmetric conflicts, survival itself can constitute victory.
In Frank Herbert’s Dune, the protagonist, Paul Muad’dib says “he who can destroy a thing, controls a thing.” This is the essence of Iranian strategy – they have a stranglehold on petroleum supply, and can destroy the world economy. Trump has had to loosen sanctions on both Iran’s and Russia’s oil, simply to prevent economic collapse.
The Ramadan War has already reshaped regional dynamics. Whether it reshapes global power structures will depend on how the next phase unfolds, and whether the United States is willing to pay the price required to achieve its aims.
by Vinod Moonesinghe
Features
Nayanandaya:A literary autopsy of Sri Lanka’s Middle Class
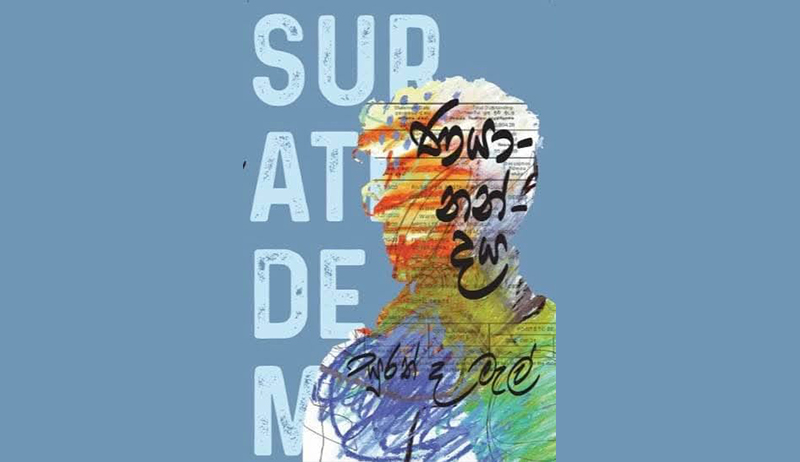
“Nayanandaya,” meaning the enchantment of indebtedness, is Surath de Mel’s latest novel. True to his reputation as a maximalist writer, de Mel traverses the labyrinth of middle-class struggles; poverty, unemployment, the quest for education, through a father’s fragile dreams. The novel unfolds around Mahela, his son, his friendships, and the fragile relationships that keep him tethered to life.
“Happiness is not a destination; it is a journey. There are no shortcuts to it. At some point, the path you thought was right will be wrong. You have to make sacrifices for it.”
These words, uttered by the protagonist Mahela to his ten-year-old son, is the silent mantra of every middle-class parent. A common urban middle-class father’s yearning for his child to climb the ladder he himself could not ascend.
A Socio-Political Mirror
Sri Lanka’s middle class remains trapped in paradox. They are educated but underemployed, salaried but indebted, socially respected yet politically invisible. Structural inequalities, economic volatility and populist politics inclusively contribute to keep them “forever middle”.
Through protagonist Mahela, who is sometimes a graphic designer, sometimes a vendor and always a failure Surath de Mel sketches the deficiencies of an education system that does not nurture skills of the students. Sri Lanka boasts about high literacy rates, yet the economy cannot absorb the thousands of graduates produced into meaningful work. Underemployment becomes the inheritance of the middle class. With political connections often the stories can be transformed. De Mel pens it in dark humour to expose these truths:
“Some notorious writer once sneered in a newspaper, ‘Give your ass to the minister, and you’ll earn the right to keep it on a bigger chair.’ Countless people waiting in ministers’ offices, pressing
their backsides to seats, carrying the weight of their own lives.”
Childhood Trauma and Its Echoes
Surath de Mel frequently weaves psychoanalysis into his fiction. In Nayanandaya, he captures the lingering shadows of childhood trauma. Mahela, scarred by a loveless and fractured youth, suffers phobic anxiety and depression, apparently with a personality disorder as an adult. His confession at the psychologist reveals it out:
“Childhood? I didn’t have one. I was fifteen when I was born.”
Here, Mahela marks his true birth not at infancy, but at the death of his parents. This statement itself reveals the childhood trauma the protagonist had gone through and the reader can attribute his subsequent psychological struggles as the cause of it.
From a Lacanian perspective, trauma is not just something that happens to a child; it is a deep break in how the child understands the world, themselves, and others. Some experiences are too painful to be put into words. Lacan calls this the Real — what cannot be fully spoken or explained. This pain does not disappear but returns later in life as anxiety, fear, or obsessive compulsive disorder.
This trauma disturbs the child’s sense of self and their place in society. When language fails to make sense of loss, the mind creates fantasies to survive. These fantasies quietly shape adult desires, relationships, and choices.
In Nayanandaya, childhood trauma of the protagonist does not stay buried — it lives on, shaping the adulthood in unseen ways. In the narrative, Mahela’s struggles are not just personal failures but the result of a past that was never given words.
Tears of Fathers – Forgotten in Sri Lankan Literature
Sri Lankan literature has long been attentive to suffering — especially rural poverty, social injustice, and the silent endurance of women and single mothers. Countless novels, poems, and songs have given voice to maternal sacrifice, female resilience, and women’s oppression.
Yet, within this rich narratives, the quiet grief of the urban middle-class father remains mostly unseen. Rarely does fiction pause to examine the emotional lives of men who shoulder responsibility without language for their pain. These masculine tears are private, swallowed by routinely and masked by humour or silence. Definitely never granted literary space.
In Nayanandaya, Surath de Mel breaks this silence. Through Mahela, he lends voice to these overlooked men — fathers whose love is expressed through sacrifice rather than speech. However, de Mel does not romanticise the tears. Rather he humanises them. He allows their vulnerabilities, anxieties, and quiet despair to surface with honesty and compassion. In doing so, Nayanandaya fills a striking gap in Sri Lankan literature, reminding us that fathers, too, carry invisible wounds.
Literary value
With Nayanandaya, Surath de Mel reaches a new pinnacle in his literary craft. His language is dense yet lyrical, enriched with similes, metaphors, irony, and a full range of literary tools deployed with confidence and control.
One of the novel’s most touching narrative choices is the personification of Mahela’s son’s soft toy, Wonie. Through personified Wonie, de Mel captures the two most touching incidents in the entire novel . This simply reveals the author’s artistic maturity, transforming a simple object into a powerful emotional conduit that anchors the novel’s tenderness amidst its despair.
At a deeper symbolic level, Mahela himself can be read as more than an individual character, but a metaphor for Sri Lanka — a nation struggling under economic hardship, clinging to impractical dreams, witnessing the migration of its people, and drifting towards a slow, painful exhaustion. His personal failures could mirror the broader decay of social and economic structures. This symbolic reading lends Nayanandaya a haunting national resonance.
Today, many write and many publish, but only a few transform language into literature that lingers in the reader’s mind long after the final page. Surath de Mel belongs to that rare few. In a literary landscape crowded with voices, he remains devoted to art rather than popularity or trend. As a scholar of Sinhala language and literature, de Mel writes with intellectual depth, dark humour, and deep human empathy.
In conclusion, Nayanandaya is not merely a story; it is social commentary, psychoanalytic reflection, and tragic poetry woven into richly textured prose. With this novel — a masterful interlacing of love, debt, and fragile dreams — Surath de Mel engraves a distinctly Dostoevskian signature into Sinhala literature.
Reviewed by Dr. Charuni Kohombange
Features
Domestic Energy Saving
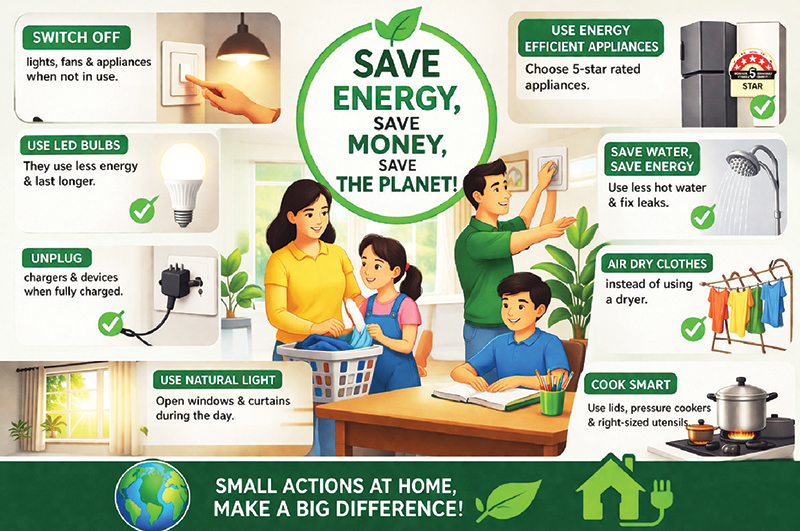
Around 40 percent of the annual energy we use is consumed in domestic activities. Energy is costly, and supply is not unlimited. Unfortunately, we realize the importance of energy – saving only during the time of a crisis.
If you adopt readily affordable energy-saving strategies, you will cut down your living expenditure substantially, relieving the energy burden of the nation. Here are some tips.
Cooking:
Cooking consumes a good portion of domestic energy demand and common practices, and negligence leads to 30 – 40 percent wastage. A simple experiment revealed that the energy expenditure in boiling an egg with the usual unnecessary excess water in an open pan is nearly 50 percent higher than boiling in a closed lid pan with the minimal amount of water. In an open pan, a large quantity of heat is lost via convection currents and expulsion of water vapor, carrying excessive amounts of heat energy (latent heat of vaporisation). Still, most of us boil potatoes for prolonged intervals of time in open receptacles, failing to realise that it is faster and more efficient to boil potatoes or any other food material in a closed pan. About 30 – 40 percent of domestic cooking energy requirements can be cut down by cooking in closed-lid pans. Furthermore, food cooked in closed pans is healthier because of less mixing with air that causes food oxidation. Fat oxidation generates toxic substances. In a closed- lid utensil (not tightly closed), food is covered with a blanket of water vapor at a positive pressure, preventing entry of air and therefore food oxidation.
Overcooking is another bad habit that not only wastes energy but also degrades the nutritional value of food.
Electric kettle:
For making morning or evening tea or preparing tea to serve a visitor. Do not pour an unnecessarily large quantity of water into the electric kettle. Note that the energy needed to make 10 cups of tea is ten times that of one cup.
Electric Ovens:
Avoid the use of electric ovens as far as possible. Remember that foods cooked at higher temperatures are generally unhealthy, and even carcinogens are formed when food is fried at higher temperatures in an oven. If ever you need to bake something in an oven, limit the number of times you open the door. Use smaller ovens adequate for the purpose and not larger ones just for fashion.
Refrigerators:
Refrigerators consume lots of energy. Do not use over-capacity refrigerators just for fashion. Every time you open the fridge, more electricity is used to reset the cooling temperature. Plan your access to the appliance accordingly. Check whether the doors are properly secured and there are no leakages. Keep the fridge in a cooler location, not hit by direct sunlight and away from warmer places in the kitchen. Remember that turning off the fridge frequently will not save energy, instead it draws more energy.
Use of gas burners:
Do not use oversized utensils. Keep the lid closed as far as possible to prevent the escape of heat. Remember that excessive amounts of heat energy are carried away by a large surface-area conducting utensil. Do not open the gas vent to allow the flame to flash outside the vessel. A flame not impinging on the pan would not heat it, and gas is wasted. Ensure that the flame is blue. Frequently check whether gas vents are clogged with rust and carbon. Frequently, cooking material in the pan drops into the gas vents, and salt there corrodes the gas vents. Cleaning and washing would be necessary. Do not prolong cooking, taking time to prepare ingredients and adding them to the pan intermittently. Add ingredients at once and before switching the burner. If the preparation of a dish is prolonged to slow the cooking, use earthenware pots rather than metallic ones. An earthenware pot, being thermally less conducting retain heat.
Firewood for cooking:
Do not attempt to eliminate the use of firewood in cooking. If you are living in a village area, the exclusive use of LPG gas is an unnecessary expenditure. Large smoke-free, efficient oven designs are now available. If you are compelled to use gas, keep the option of firewood ovens, especially for prolonged cooking. Admittedly, there are locations, especially in cities, where the use of firewood is unsuited.
Hot water showers:
Before installing hot water showers, reconsider whether they are really necessary in a hot tropical climate. Go for solar water heaters, although the installation cost is high. Instant water heaters consume much less electricity compared to geysers with water tanks. Now, cheap and safe instant water heaters are available.
Lighting:
Arrange and design your residence to optimise daytime illumination until late evening. If you are constructing a new house, take this issue into account. Use LED lamps, which provide the same illumination for 85 percent less energy. In study rooms and areas that require prolonged illumination, paint the walls white. Angle – poised LED lamps with very low voltage are available. Use them for reading and studies. Routinely clean the surfaces of all lamps. Dust deposition cuts off light.
Air conditioning and ventilation:
Air conditioning consumes prohibitively large quantities of electrical energy. You can avoid air conditioning by optimising ventilation. The principle is to have air entry points (windows) in the house near the ground level and exit points (vents or windows) near the roof. Ground level is cooler, and the region near the roof is warmer. Thus, a cool air current enters the house near the ground level and hot air is drawn by the vents near the roof. The region near the ground can be rendered cooler by planting trees. Architectural designs are available to optimise this effect. You can sense the direction of air motion by holding a thin strip of paper near the windows at the ground and near the roof level. In addition to ceiling fan, install exhaust fans in the upper points of the house to remove hot air and draw cooler air through windows near the ground. Reduce the amount of sunlight hitting the roof by shading with trees. There are techniques for increasing the reflectance of the roof with paints and other designs.
Transportation:
A good portion of your budget is drained by transportation. Irrespective of who you are, use public transport if convenient and available. As much as possible, use the telephone and email to get your things done. If the officers do not comply for no valid reason, complain. Plan your trips to the town to do several things at the same time. Whenever possible, plan to share transport. Buy energy – efficient small vehicles. Routinely examine your vehicle for energy efficiency, i.e. correct tire pressure etc.
Charge electric vehicles off peak hours. Slow charging reduces heat generation in the circuit, reducing energy loss.
Energy is costly and limited in supply. Everything you do consumes energy. Be energy conscious in all your deeds. That attitude will reduce your expenditure, lessen the environmental degradation and financial burden of the nation in importing fuel.
Educating the general public is the most effective way of implementing energy-saving strategies.
By Prof. Kirthi Tennakone
(kenna@yahoo.co.uk)
-

 News4 days ago
News4 days agoTariff shock from 01 April as power costs climb across the board
-
 News2 days ago
News2 days ago2025 GCE AL: 62% qualify for Uni entrance; results of 111 suspended
-

 News5 days ago
News5 days agoInquiry into female employee’s complaint: Retired HC Judge’s recommendations ignored
-
 Features6 days ago
Features6 days agoWhen seabed goes dark: The Persian Gulf, cable sabotage, and race for space-based monopoly
-

 Features5 days ago
Features5 days agoNew arithmetic of conflict: How the drone revolution is inverting economics of war
-

 Business3 days ago
Business3 days agoHour of reckoning comes for SL’s power sector
-

 Editorial2 days ago
Editorial2 days agoSearch for Easter Sunday terror mastermind
-

 Sports5 days ago
Sports5 days agoSri Lanka’s 1996 World Cup heroes to play exhibition match in Kuala Lumpur