Features
The Lazarus heist: How North Korea almost pulled off a billion-dollar hack
In 2016 North Korean hackers planned a $1bn raid on Bangladesh’s national bank and came within an inch of success – it was only by a fluke that all but $81m of the transfers were halted, report Geoff White and Jean H Lee. But how did one of the world’s poorest and most isolated countries train a team of elite cyber-criminals?
It all started with a malfunctioning printer. It’s just part of modern life, and so when it happened to staff at Bangladesh Bank they thought the same thing most of us do: another day, another tech headache. It didn’t seem like a big deal.
But this wasn’t just any printer, and it wasn’t just any bank.
Bangladesh Bank is the country’s central bank, responsible for overseeing the precious currency reserves of a country where millions live in poverty.
And the printer played a pivotal role. It was located inside a highly secure room on the 10th floor of the bank’s main office in Dhaka, the capital. Its job was to print out records of the multi-million-dollar transfers flowing in and out of the bank.
When staff found it wasn’t working, at 08:45 on Friday 5 February 2016, “we assumed it was a common problem just like any other day,” duty manager Zubair Bin Huda later told police. “Such glitches had happened before.”
In fact, this was the first indication that Bangladesh Bank was in a lot of trouble. Hackers had broken into its computer networks, and at that very moment were carrying out the most audacious cyber-attack ever attempted. Their goal: to steal a billion dollars.
To spirit the money away, the gang behind the heist would use fake bank accounts, charities, casinos and a wide network of accomplices.
But who were these hackers and where were they from?
According to investigators the digital fingerprints point in just one direction: to the government of North Korea.
SPOILER ALERT: This is the story told in the 10-episode BBC World Service podcast, The Lazarus Heist.
That North Korea would be the prime suspect in a case of cyber-crime might to some be a surprise. It’s one of the world’s poorest countries, and largely disconnected from the global community – technologically, economically, and in almost every other way.
And yet, according to the FBI, the audacious Bangladesh Bank hack was the culmination of years of methodical preparation by a shadowy team of hackers and middlemen across Asia, operating with the support of the North Korean regime.
In the cyber-security industry the North Korean hackers are known as the Lazarus Group, a reference to a biblical figure who came back from the dead; experts who tackled the group’s computer viruses found they were equally resilient.
Little is known about the group, though the FBI has painted a detailed portrait of one suspect: Park Jin-hyok, who also has gone by the names Pak Jin-hek and Park Kwang-jin.
It describes him as a computer programmer who graduated from one of the country’s top universities and went to work for a North Korean company, Chosun Expo, in the Chinese port city of Dalian, creating online gaming and gambling programs for clients around the world.
While in Dalian, he set up an email address, created a CV, and used social media to build a network of contacts. Cyber-footprints put him in Dalian as early as 2002 and off and on until 2
013 or 2014, when his internet activity appears to come from the North Korean capital, Pyongyang, according to an FBI investigator’s affidavit.
The agency has released a photo plucked from a 2011 email sent by a Chosun Expo manager introducing Park to an outside client. It shows a clean-cut Korean man in his late 20s or early 30s, dressed in a pin-striped black shirt and chocolate-brown suit. Nothing out of the ordinary, at first glance, apart from a drained look on his face.
But the FBI says that while he worked as a programmer by day, he was a hacker by night.
In June 2018, US authorities charged Park with one count of conspiracy to commit computer fraud and abuse, and one count of conspiracy to commit wire fraud (fraud involving mail, or electronic communication) between September 2014 and August 2017. He faces up to 20 years in prison if he is ever tracked down. (He returned from China to North Korea four years before the charges were filed.)
But Park, if that is his real name, didn’t become a hacker for the state overnight. He is one of thousands of young North Koreans who have been cultivated from childhood to become cyber-warriors – talented mathematicians as young as 12 taken from their schools and sent to the capital, where they are given intensive tuition from morning till night.
When the bank’s staff rebooted the printer, they got some very worrying news. Spilling out of it were urgent messages from the Federal Reserve Bank in New York – the “Fed” – where Bangladesh keeps a US-dollar account. The Fed had received instructions, apparently from Bangladesh Bank, to drain the entire account – close to a billion dollars.
The Bangladeshis tried to contact the Fed for clarification, but thanks to the hackers’ very careful timing, they couldn’t get through.
The hack started at around 20:00 Bangladesh time on Thursday 4 February. But in New York it was Thursday morning, giving the Fed plenty of time to (unwittingly) carry out the hackers’ wishes while Bangladesh was asleep.
The next day, Friday, was the start of the Bangladeshi weekend, which runs from Friday to Saturday. So the bank’s HQ in Dhaka was beginning two days off. And when the Bangladeshis began to uncover the theft on Saturday, it was already the weekend in New York.
“So you see the elegance of the attack,” says US-based cyber-security expert Rakesh Asthana. “The date of Thursday night has a very defined purpose. On Friday New York is working, and Bangladesh Bank is off. By the time Bangladesh Bank comes back on line, the Federal Reserve Bank is off. So it delayed the whole discovery by almost three days.”
And the hackers had another trick up their sleeve to buy even more time. Once they had transferred the money out of the Fed, they needed to send it somewhere. So they wired it to accounts they’d set up in Manila, the capital of the Philippines. And in 2016, Monday 8 February was the first day of the Lunar New Year, a national holiday across Asia.
By exploiting time differences between Bangladesh, New York and the Philippines, the hackers had engineered a clear five-day run to get the money away.
They had had plenty of time to plan all of this, because it turns out the Lazarus Group had been lurking inside Bangladesh Bank’s computer systems for a year.
In January 2015, an innocuous-looking email had been sent to several Bangladesh Bank employees. It came from a job seeker calling himself Rasel Ahlam. His polite enquiry included an invitation to download his CV and cover letter from a website. In reality, Rasel did not exist – he was simply a cover name being used by the Lazarus Group, according to FBI investigators. At least one person inside the bank fell for the trick, downloaded the documents, and got infected with the viruses hidden inside.
Once inside the bank’s systems, Lazarus Group began stealthily hopping from computer to computer, working their way towards the digital vaults and the billions of dollars they contained.
And then they stopped.
Why did the hackers only steal the money a whole year after the initial phishing email arrived at the bank? Why risk being discovered while hiding inside the bank’s systems all that time? Because, it seems, they needed the time to line up their escape routes for the money.
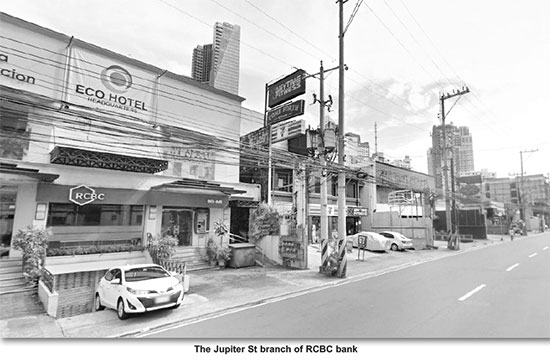
Jupiter Street is a busy thoroughfare in Manila. Next to an eco-hotel and a dental surgery is a branch of RCBC, one of the country’s largest banks. In May 2015, a few months after the hackers accessed Bangladesh Bank’s systems, four accounts were set up here by the hackers’ accomplices. In hindsight, there were some suspicious signs: the driver’s licences used to set up the accounts were fakes, and the applicants all claimed to have exactly the same job title and salary, despite working at different companies. But no-one seemed to notice. For months the accounts sat dormant with their initial $500 deposit untouched while the hackers worked on other aspects of the plan.
By February 2016, having successfully hacked into Bangladesh Bank and created conduits for the money, the Lazarus Group was ready.
But they still had one final hurdle to clear – the printer on the 10th floor. Bangladesh Bank had created a paper back-up system to record all transfers made from its accounts. This record of transactions risked exposing the hackers’ work instantly. And so they hacked into the software controlling it and took it out of action.
With their tracks covered, at 20:36 on Thursday 4 February 2016, the hackers began making their transfers – 35 in all, totalling $951m, almost the entire contents of Bangladesh Bank’s New York Fed account. The thieves were on their way to a massive payday – but just as in a Hollywood heist movie, a single, tiny detail would catch them out.
As Bangladesh Bank discovered the missing money over the course of that weekend, they struggled to work out what had happened. The bank’s governor knew Rakesh Asthana and his company, World Informatix, and called him in for help. At this point, Asthana says, the governor still thought he could claw back the stolen money. As a result, he kept the hack secret – not just from the public, but even from his own government.
Meanwhile, Asthana was discovering just how deep the hack went. He found out the thieves had gained access to a key part of Bangladesh Bank’s systems, called Swift. It’s the system used by thousands of banks around the world to co-ordinate transfers of large sums between themselves. The hackers didn’t exploit a vulnerability in Swift – they didn’t need to – so as far as Swift’s software was concerned the hackers looked like genuine bank employees.
It soon became clear to Bangladesh Bank’s officials that the transactions couldn’t just be reversed. Some money had already arrived in the Philippines, where the authorities told them they would need a court order to start the process to reclaim it. Court orders are public documents, and so when Bangladesh Bank finally filed its case in late February, the story went public and exploded worldwide.
The consequences for the bank’s governor were almost instant. “He was asked to resign,” says Asthana. “I never saw him again.”
US Congresswoman Carolyn Maloney remembers clearly where she was when she first heard about the raid on Bangladesh Bank. “I was leaving Congress and going to the airport and reading about the heist, and it was fascinating, shocking – a terrifying incident, probably one of the most terrifying that I’ve ever seen for financial markets.”
As a member of the congressional Committee on Financial Services, Maloney saw the bigger picture: with Swift underpinning so many billions of dollars of global trade, a hack like this could fatally undermine confidence in the system.
She was particularly concerned by the involvement of the Federal Reserve Bank. “They were the New York Fed, which usually is so careful. How in the world did these transfers happen?”
Maloney contacted the Fed, and staff explained to her that most of the transfers had in fact been prevented – thanks to a tiny, coincidental detail.
The RCBC bank branch in Manila to which the hackers tried to transfer $951m was in Jupiter Street. There are hundreds of banks in Manila that the hackers could have used, but they chose this one – and the decision cost them hundreds of millions of dollars.
“The transactions… were held up at the Fed because the address used in one of the orders included the word ‘Jupiter’, which is also the name of a sanctioned Iranian shipping vessel,” says Carolyn Maloney.
Just the mention of the word “Jupiter” was enough to set alarm bells ringing in the Fed’s automated computer systems. The payments were reviewed, and most were stopped. But not all. Five transactions, worth $101m, crossed this hurdle.
Of that, $20m was transferred to a Sri Lankan charity called the Shalika Foundation, which had been lined up by the hackers’ accomplices as one conduit for the stolen money. (Its founder, Shalika Perera, says she believed the money was a legitimate donation.) But here again, a tiny detail derailed the hackers’ plans. The transfer was made to the “Shalika Fundation”. An eagle-eyed bank employee spotted the spelling mistake and the transaction was reversed.
And so $81m got through. Not what the hackers were aiming for, but the lost money was still a huge blow for Bangladesh, a country where one in five people lives below the poverty line.
By the time Bangladesh Bank began its efforts to claw the money back, the hackers had already taken steps to make sure it stayed beyond reach.
On Friday 5 February, the four accounts set up the previous year at the RCBC branch in Jupiter Street suddenly sprang to life.
The money was transferred between accounts, sent to a currency exchange firm, swapped into local currency and re-deposited at the bank. Some of it was withdrawn in cash. For experts in money laundering, this behaviour makes perfect sense.
“You have to make all of that criminally derived money look clean and look like it has been derived from legitimate sources in order to protect whatever you do with the money afterwards,” says Moyara Ruehsen, director of the Financial Crime Management Programme at the Middlebury Institute of International Studies in Monterey, California. “You want to make the money trail as muddy and obscure as possible.”
Even so, it was still possible for investigators to trace the path of the money. To make it completely untrackable it had to leave the banking system.
The Solaire sits on the waterfront in Manila, a gleaming white palace of hedonism, home to a hotel, a huge theatre, high-end shops and – its most famous attraction – a sprawling casino floor. Manila has become a big draw for gamblers from mainland China, where the pastime is illegal, and the Solaire is “one of the most elegant casino floors in Asia”, according to Mohammed Cohen, editor-at-large of Inside Asian Gaming Magazine. “It’s really beautifully designed, comparable to anything in south-east Asia. It has roughly 400 gaming tables and about 2,000 slot machines.”
It was here in Manila’s glitzy casino scene that the Bangladesh Bank thieves mounted the next stage of their money laundering operation. Of the $81m that washed through the RCBC bank, $50m was deposited in accounts at the Solaire and another casino, the Midas. (What happened to the other $31m? According to a Philippines Senate Committee set up to investigate, it was paid to a Chinese man called Xu Weikang, who’s believed to have left town on a private jet and never been heard of since.)
The idea of using casinos was to break the chain of traceability. Once the stolen money had been converted into casino chips, gambled over the tables, and changed back into cash, it would be almost impossible for investigators to trace it.
But what about the risks? Aren’t the thieves in danger of losing the loot across the casino tables? Not at all.
Firstly, instead of playing in the public parts of the casino, the thieves booked private rooms and filled them with accomplices who would play at the tables; this gave them control over how the money was gambled. Secondly, they used the stolen money to play Baccarat – a wildly popular game in Asia, but also a very simple one. There are only three outcomes on which to bet, and a relatively experienced player can recoup 90% or more of their stake (an excellent outcome for money launderers, who often get a far smaller return). The criminals could now launder the stolen funds and look forward to a healthy return – but to do so would take careful management of the players and their bets, and that took time. For weeks, the gamblers sat inside Manila’s casinos, washing the money.
Bangladesh Bank, meanwhile, was catching up. Its officials had visited Manila and identified the money trail. But when it came to the casinos, they hit a brick wall. At that time, the Philippines gambling houses were not covered by money laundering regulations. So far as the casinos were concerned, the cash had been deposited by legitimate gamblers, who had every right to fritter it away over the tables. (The Solaire casino says it had no idea it was dealing with stolen funds, and is co-operating with the authorities. The Midas did not respond to requests for comment.)
The bank’s officials managed to recover $16m of the stolen money from one of the men who organised the gambling jaunts at the Midas casino, called Kim Wong. He was charged, but the charges were later dropped. The rest of the money, however – $34m – was leaching away. Its next stop, according to investigators, would take it one step closer to North Korea.
Macau is an enclave of China, similar in constitution to Hong Kong. Like the Philippines, it’s a hotspot for gambling and home to some of the world’s most prestigious casinos. The country also has long-established links to North Korea. It was here that North Korean officials were in the early 2000s caught laundering counterfeit $100 notes of extremely high quality – so-called “Superdollars” – which US authorities claim were printed in North Korea. The local bank they laundered them through was eventually placed on a US sanctions list thanks to its connections with the Pyongyang regime.
It was also in Macau that a North Korean spy was trained before she bombed a Korean Air flight in 1987, killing 115 people. And it was in Macau that Kim Jong-un’s half brother, Kim Jong-nam, lived in exile before being fatally poisoned in Malaysia in an assassination many believe was authorised personally by the North Korean leader.
As the money stolen from Bangladesh Bank was laundered through the Philippines, numerous links to Macau started to emerge. Several of the men who organised the gambling jaunts in the Solaire were traced back to Macau. Two of the companies that had booked the private gambling rooms were also based in Macau. Investigators believe most of the stolen money ended up in this tiny Chinese territory, before being sent back to North Korea.
At night, North Korea famously appears to be a black hole in photos taken from outer space by Nasa, due to the lack of electricity in most parts of the country – in stark contrast to South Korea, which explodes with light at all hours of the day and night. North Korea ranks among the 12 poorest nations in the world, with an estimated GDP of just $1,700 per person – less than Sierra Leone and Afghanistan, according to the CIA.
And yet North Korea has produced some of the world’s most brazen and sophisticated hackers, it appears.
Understanding how, and why, North Korea has managed to cultivate elite cyber-warfare units requires looking at the family that has ruled North Korea since its inception as a modern nation in 1948: the Kims.
Founder Kim Il-sung built the nation officially known as the Democratic People’s Republic of Korea on a political system that is socialist but operates more like a monarchy.
His son, Kim Jong-il, relied on the military as his power base, provoking the US with tests of ballistic missile and nuclear devices. In order to fund the programme, the regime turned to illicit methods, according to US authorities – including the highly sophisticated counterfeit Superdollars.
Kim Jong-il also decided early on to incorporate cyber into the country’s strategy, establishing the Korea Computer Centre in 1990. It remains the heart of the country’s IT operations.
When, in 2010, Kim Jong-un – Kim Jong-il’s third son – was revealed as his heir apparent, the regime unfurled a campaign to portray the future leader, only in his mid-20s and unknown to his people, as a champion of science and technology. It was a campaign designed to secure his generation’s loyalty and to inspire them to become his warriors, using these new tools.
The young Kim, who took power in late 2011 upon his father’s death, called nuclear weapons a “treasured sword”, but he too needed a way to fund them – a task complicated by the ever tighter sanctions imposed by the UN Security Council after the country’s first tests of a nuclear device and a long-range ballistic missile in 2006. Hacking was one solution, US authorities say.
The embrace of science and technology did not extend to allowing North Koreans to freely connect to the global internet, though – that would enable too many to see what the world looks like outside their borders, and to read accounts that contradict the official mythology.
So in order to train its cyber-warriors, the regime sends the most talented computer programmers abroad, mostly to China.
There they learn how the rest of the world uses computers and the internet: to shop, to gamble, to network and to be entertained. It’s there, experts say, that they are transformed from mathematical geniuses into hackers.
Scores of these young men are believed to live and work in North Korean-run outposts in China.
“They are very good at masking their tracks but sometimes, just like any other criminal, they leave crumbs, evidence behind,” says Kyung-jin Kim, a former FBI Korea chief who now works as a private sector investigator in Seoul. “And we’re able to identify their IP addresses back to their location.”
Those crumbs led investigators to an unassuming hotel in Shenyang, in China’s north-east, guarded by a pair of stone tigers, a traditional Korean motif. The hotel was called the Chilbosan, after a famous mountain range in North Korea.
Photos posted to hotel review sites such as Agoda reveal charming Korean touches: colourful bedspreads, North Korean cuisine and waitresses who sing and dance for their customers.
It was “well-known in the intel community”, says Kyung-jin Kim, that suspected North Korean hackers were operating from the Chilbosan when they first broke on to the world stage in 2014.
Meanwhile, in the Chinese city of Dalian, where Park Jin-hyok is believed to have lived for a decade, a community of computer programmers was living and working in a similar North-Korea-run operation, says defector Hyun-seung Lee.
Lee was born and raised in Pyongyang but lived for years in Dalian, where his father was a well-connected businessman working for the North Korean government – until the family defected in 2014. The bustling port city across the Yellow Sea from North Korea was home to about 500 North Koreans when he was living there, Lee says.
Among them, more than 60 were programmers – young men he got to know, he says, when North Koreans gathered for national holidays, such as Kim Il-sung’s birthday.
One of them invited him over to their living quarters. There, Lee saw “about 20 people living together and in one space. So, four-to-six people living in one room, and then the living room they made it like an office – all the computers, all in the living room.”
They showed him what they were producing: mobile phone games that they were selling to South Korea and Japan through brokers, making $1m per year.
Although North Korean security officials kept a close eye on them, life for these young men was still relatively free.
“It’s still restricted, but compared to North Korea, they have much freedom so that they can access the internet and then they can watch some movies,” Lee says.
After about eight years in Dalian, Park Jin-hyok appears to have been anxious to return to Pyongyang. In a 2011 email intercepted by the FBI, he mentions wanting to marry his fiancee. But it would be a few more years before he was allowed to do this.
The FBI says his superiors had another mission for him: a cyber-attack on one of the world’s largest entertainment companies – Sony Pictures Entertainment in Los Angeles, California. Hollywood.
In 2013, Sony Pictures announced the making of a new movie starring Seth Rogen and James Franco that would be set in North Korea.
It’s about a talk show host, played by Franco, and his producer, played by Rogen. They go to North Korea to interview Kim Jong-un, and are persuaded by the CIA to assassinate him.
North Korea threatened retaliatory action against the US if Sony Pictures Entertainment released the film, and in November 2014 an email was sent to company bosses from hackers calling themselves the Guardians of Peace, threatening to do “great damage”.
Three days later a horror-film image of a blood-red skeleton with fangs and glaring eyes appeared on employees’ computer screens. The hackers had made good on their threats. Executives’ salaries, confidential internal emails, and details of as-yet unreleased films were leaked online – and the company’s activities ground to a halt as its computers were disabled by the hackers’ viruses. Staff couldn’t swipe passes to enter their offices or use printers. For a full six weeks a coffee shop on the MGM lot, the HQ of Sony Pictures Entertainment, was unable to take credit cards.
Sony had initially pressed ahead with plans to release The Interview in the usual way, but these were hastily cancelled when the hackers threatened physical violence. Mainstream cinema chains said they wouldn’t show the film, so it was released only digitally and in some independent cinemas.
But the Sony attack, it turns out, may have been a dry run for an even more ambitious hack – the 2016 bank heist in Bangladesh.
Bangladesh is still trying to recover the rest of its stolen money – around $65m. Its national bank is taking legal action against dozens of people and institutions, including RCBC bank, which denies breaching any rules.
As skilful as the hacking of Bangladesh Bank was, just how pleased would the Pyongyang regime have been with the end result? After all, the plot started out as a billion-dollar heist, and the eventual haul would have been only in the tens of millions. Hundreds of millions of dollars had been lost as the thieves had navigated the global banking system, and tens of millions more as they paid off middlemen. In future, according to US authorities, North Korea would find a way to avoid this attrition.
In May 2017, the WannaCry ransomware outbreak spread like wildfire, scrambling victims’ files and charging them a ransom of several hundred dollars to retrieve their data, paid using the virtual currency Bitcoin. In the UK, the National Health Service was particularly badly hit; accident and emergency departments were affected, and urgent cancer appointments had to be rescheduled.
As investigators from the UK’s National Crime Agency delved into the code, working with the FBI, they found striking similarities with the viruses used to hack into Bangladesh Bank and Sony Pictures Entertainment, and the FBI eventually added this attack to the charges against Park Jin-hyok. If the FBI’s allegations are correct, it shows North Korea’s cyber army had now embraced cryptocurrency – a vital leap forward because this high-tech new form of money largely bypasses the traditional banking system – and could therefore avoid costly overheads, such as pay-offs to middlemen.
WannaCry was just the start. In the ensuing years, tech security firms have attributed many more cryptocurrency attacks to North Korea. They claim the country’s hackers have targeted exchanges where cryptocurrencies like Bitcoin are swapped for traditional currencies. Added together, some estimates put the thefts from these exchanges at more than $2bn.
And the allegations keep coming. In February the US Department of Justice charged two other North Koreans, whom they claim are also members of the Lazarus Group and are linked to a money-laundering network stretching from Canada to Nigeria.
Computer hacking, global money laundering, cutting edge cryptocurrency thefts… If the allegations against North Korea are true, then it appears many people have underestimated the country’s technical skill and the danger it presents.
But this also paints a disturbing picture of the dynamics of power in our increasingly connected world, and our vulnerability to what security experts call “asymmetric threat” – the ability of a smaller adversary to exercise power in novel ways that make it a far bigger threat than its size would indicate.
Investigators have uncovered how a tiny, desperately poor nation can silently reach into the email inboxes and bank accounts of the rich and powerful thousands of miles away. They can exploit that access to wreak havoc on their victims’ economic and professional lives, and drag their reputations through the mud. This is the new front line in a global battleground: a murky nexus of crime, espionage and nation-state power-mongering. And it’s growing fast.
Geoff White is the author of Crime Dot Com: From Viruses to Vote Rigging, How Hacking Went Global. Jean H Lee opened Associated Press’s Pyongyang bureau in 2012; she is now a senior fellow at the Wilson Center in Washington DC.
– BBC News
Features
New arithmetic of conflict: How the drone revolution is inverting economics of war

The contemporary global landscape is currently defined by two distinct but interconnected theaters of conflict that are fundamentally reshaping the future of military engagement, as noted by political analyst Fareed Zakaria. This shifts the advantage toward smaller states, or even non-state actors, who do not need to defeat a superpower in direct confrontation; they only need to sustain a constant level of low-cost harassment. In the Middle East, the escalating tensions between the United States and Iran have moved beyond traditional brinkmanship into a high-stakes confrontation centred on the Strait of Hormuz and regional infrastructure. This direction is characterised by Iran’s sophisticated use of asymmetric ‘precise mass’ to challenge American naval and technological superiority, forcing a re-evaluation of how a superpower maintains deterrence against a revolutionary regime that views its own hardware as expendable. This theatre serves as a primary example of how a medium-sized power can utilise low-cost, high-volume technology to neutralize the traditional advantages of a much wealthier adversary, potentially driving the region toward a dangerous nuclear threshold as conventional red lines are blurred.
Simultaneously, the war between Ukraine and Russia has become the world’s preeminent laboratory for the digital transformation of the battlefield. The direction of this conflict has shifted from a 20th-century war of attrition into a 21st-century war of algorithms, where the most critical ammunition is no longer just artillery shells, but data and software. Ukraine’s rapid adaptation—turning commercial drones into precision interceptors and using AI to process millions of combat images—has created a template for modern survival against a larger industrial power. Together, these two conflicts signal a global transition where the ‘exquisite’ military models of the past are being dismantled by the ‘new arithmetic’ of mass-produced precision. This essay examines how the inversion of war economics in these regions is ensuring that future supremacy will not belong to those with the most expensive platforms, but to those who can master the integration of industrial-scale with near-real-time software intelligence.
Fundamental departure
The ‘New Arithmetic of Conflict’ represents a fundamental departure from the 20th-century military paradigm, shifting the focus from high-cost, high-performance ‘exquisite’ systems to the power of ‘precise mass.’ For the last 50 years, military supremacy—particularly for the United States and its allies—has been defined by technologically superior platforms, such as the F-35 fighter jet or the Tomahawk cruise missile. While these systems are undeniably magnificent in their capabilities, they are also incredibly costly and irreplaceable in the short term. Because they take years to design and manufacture, losing even a handful in active combat is strategically damaging and painful for a modern military. This old model relied on a limited number of high-end assets that were slow to produce and even slower to replace, creating a vulnerability that smaller, more agile adversaries have now begun to exploit.
This traditional economic model is being turned upside down by the rise of cheap, commercial-off-the-shelf technology that achieves results previously reserved for superpower budgets. The emergence of the Shahed-type drone, which costs approximately $35,000, illustrates this shift perfectly. Unlike a $2 million cruise missile, these ‘one-way’ drones are built from common parts and can be launched in massive swarms. This creates a state of ‘precise mass,’ where the sheer volume of incoming, low-cost threats can overwhelm even the most sophisticated and expensive defence systems. The attacker no longer needs a massive industrial base to strike with precision; they only need the ability to scale simple, autonomous hardware.
Perhaps the most radical aspect of this inversion is the ‘cost-exchange ratio’ between attack and defence. In the past, an attacker generally had to spend more to destroy a target than a defender spent to protect it. Today, the arithmetic favours the attacker by an order of magnitude. To intercept a single $35,000 drone, a defender may be forced to fire a Patriot interceptor missile that costs roughly $4 million. This means the defender is spending over 100 times more than the attacker just to maintain the status quo. This economic reality suggests that a wealthier nation can effectively be ‘bankrupted’ or depleted of its ammunition reserves by a much smaller state or even a non-state actor using constant, low-cost harassment.
Primary laboratory
Ukraine has served as the primary laboratory for this new era of warfare, demonstrating that the real value in modern conflict is shifting from hardware to software and data. Ukrainian forces are producing stinging interceptor drones for as little as $2,000, capable of taking down far more expensive hardware. More importantly, they are treating battlefield data as a strategic asset, using millions of annotated images from combat flights to train drone AI. This creates a cycle of rapid wartime adaptation where lessons from the battlefield are turned into mass production in days rather than years. Ultimately, the winner of future conflicts may not be the nation with the finest individual platforms, but the one that can combine a small number of ‘exquisite’ weapons with a vast, intelligent, and cheaply networked mass of autonomous systems.
Building on the distinction between the ‘exquisite’ and the ‘expendable,’ the shift in military doctrine reflects a move away from the post-Cold War reliance on a small number of ultra-sophisticated assets toward a more resilient, high-volume architecture. For decades, Western military superiority was predicated on having the most advanced technology in the sky or on the sea, but the sheer cost and complexity of these systems have created a ‘fragility of excellence.’ When a single stealth fighter costs over $100 million, its loss is not merely a tactical setback but a national news event and a significant blow to the overall fleet’s readiness. This creates a psychological and strategic ‘risk aversion,’ where commanders may hesitate to deploy their most capable assets in high-threat environments for fear of losing an irreplaceable piece of national infrastructure.
Furthermore, the industrial reality of ‘exquisite’ systems is that they are built on highly specialised, low-volume production lines. In a high-intensity conflict, the rate of attrition—the speed at which equipment is destroyed—can quickly outpace the capacity of a modern industrial base to replace it. If a nation can only produce a few dozen advanced interceptors a year but loses hundreds of drones or missiles in a single week of combat, the mathematical deficit becomes insurmountable. This bottleneck has forced a re-evaluation of what constitutes a ‘good’ platform; the priority is shifting toward systems that are ‘good enough’ to be effective but cheap enough to be lost without compromising the mission or the budget.
In contrast to these legacy systems, the ‘expendable’ model treats hardware as a consumable resource, much like ammunition. By utilising modular designs and civilian-grade components, nations can mass-produce thousands of autonomous units that are inherently ‘attrition-tolerant.’ This does not mean the end of high-end technology, but rather its repositioning. Instead of a single $100 million jet trying to do everything, the future likely involves a ‘high-low’ mix where a few exquisite platforms act as command-and-control hubs, orchestrating vast swarms of cheap, expendable drones. This evolution ensures that even if the enemy successfully targets dozens of units, the collective network remains functional, shifting the strategic advantage back to the side that can sustain the fight through industrial scale and digital adaptability.
Concept of ‘precise mass’
The concept of ‘precise mass’ represents a strategic pivot where quantity possesses a quality of its own, enabled by the democratization of high-end technology. Historically, precision was a luxury available only to the world’s most advanced militaries, requiring specialised Guidance Systems and satellite constellations. Today, the ‘New Arithmetic’ flips this model by integrating commercial-off-the-shelf components—such as GPS chips found in smartphones and engines from hobbyist aircraft—into lethal, autonomous platforms.
This shift allows smaller states and non-state actors to achieve tactical objectives that once required a superpower’s budget, effectively levelling the playing field through the clever application of low-cost innovation.
The ‘Shahed Model’ serves as the primary case study for this transformation. By producing ‘one-way’ suicide drones for approximately $35,000 each, Iran has created a weapon that is essentially a flying piece of ammunition.
Because these drones are built from common, globally available parts, they are insulated from many traditional supply chain disruptions and can be manufactured at an industrial scale that far outpaces sophisticated cruise missiles. This approach prioritises ‘good enough’ technology—systems that are sufficiently accurate to hit a target but inexpensive enough to be deployed in staggering numbers without financial second-guessing.
The true power of this model is realised through ‘swarm tactics,’ which weaponise the mathematical limitations of modern air defences. When a country launches dozens or even hundreds of these low-cost drones simultaneously, it forces the defender into a ‘saturation’ crisis. Even the most advanced missile defence systems have a limited number of interceptors and can only track a finite number of targets at once. By flooding the airspace with cheap decoys and suicide drones, an attacker can ensure that while many units are shot down, a sufficient percentage will inevitably leak through to strike their targets. This creates a state of ‘precise mass,’ where volume becomes the ultimate delivery mechanism for precision, rendering traditional, high-cost defence umbrellas increasingly obsolete.
This evolution signifies that the era of the ‘silver bullet’—the single, perfect weapon—is giving way to the era of the ‘steel rain.’ In this new environment, the strategic advantage shifts to the side that can manage the highest rate of ‘precise attrition.’ Success is no longer measured by the technical sophistication of a single strike, but by the ability to sustain a continuous, overwhelming flow of autonomous threats that exhaust the enemy’s resources, patience, and defensive capacity.
‘Bankruptcy of the Defence’
The ‘Bankruptcy of the Defence’ represents a critical failure in the modern military-industrial complex’s ability to counter asymmetric threats. In the 20th century, the financial burden of warfare typically fell on the aggressor, who had to invest in expensive bombers or long-range missiles to penetrate a nation’s borders. Today, that economic gravity has shifted entirely. The most radical part of this inversion is the ‘cost-exchange ratio,’ a mathematical reality that turns defensive success into a financial liability. When a defender successfully intercepts a threat, they are often winning the tactical battle while simultaneously losing the economic war.
This disparity is most visible in what can be called the ‘$4 Million Solution.’ In modern conflict zones, we regularly see sophisticated air defence batteries—designed to intercept high-altitude ballistic missiles—being forced to engage low-speed, ‘suicide’ drones. Using a $4 million Patriot interceptor to neutralise a $35,000 Shahed-type drone is an unsustainable strategy. Even if the defence achieves a 100% intercept rate, the attacker is essentially ‘trading up’ in value at a staggering scale. The defender is forced to expend a finite, high-cost resource to eliminate a nearly infinite, low-cost nuisance, creating a logistical bottleneck where the supply of interceptors can never meet the demand of the swarm.
This ‘Losing Game’ fundamentally alters the grand strategy of global powers. Mathematically, when a defender is spending over 100 times more than the attacker per engagement, they are participating in a process of rapid financial and material depletion. As Fareed Zakaria notes, this ‘new arithmetic’ shifts the advantage toward smaller states, insurgent groups, or even criminal organisations. These actors do not need to defeat a superpower’s navy or air force in a direct confrontation; they only need to sustain a constant level of low-cost harassment. Over time, the cost of maintaining a ‘perfect’ defense becomes so high that it can effectively bankrupt a wealthier opponent or force them to withdraw from a region simply because the price of protection has become greater than the value of the presence.
Interceptors alone won’t do
Ultimately, this economic inversion suggests that the future of defence cannot rely on ‘exquisite’ interceptors alone. The current model is built on a scarcity of precision, but in an era where precision is mass-produced, the defense must find a way to make interception as cheap as the intrusion. Until a nation can field directed-energy weapons or low-cost kinetic interceptors that match the $35,000 price point of the threat, they remain trapped in a defensive paradigm that is both mathematically flawed and strategically exhausting.
The final piece of this military evolution is the emergence of Ukraine as the ‘Great Laboratory’ of modern warfare, where necessity has birthed a model of adaptation that operates at wartime speed. This environment has transformed the country from a passive recipient of aid into a sovereign architect of a new kind of combat. Central to this transformation is the development of the ‘STING’ interceptor drone. Produced by groups like Wild Hornets for approximately $2,000, these drones can reach speeds of 280 km/h—fast enough to chase down and destroy the lumbering Shahed drones that have plagued Ukrainian infrastructure. By mid-2025, these low-cost predators had already downed over 3,000 enemy targets, proving that a $2,000 solution could reliably neutralize a threat costing tens of thousands, further tilting the economic scales in favor of the agile defender.
However, the most significant output of this laboratory is not the hardware itself, but the data it generates. Defense Minister Mykhailo Fedorov has noted that Ukraine now possesses a unique array of battlefield data that is unmatched anywhere in the world, including millions of annotated images gathered during tens of thousands of combat flights. In a historic move, Ukraine has begun opening access to this ‘digital ammunition’ through a dedicated AI platform. This allows international partners and defense firms to train their algorithms on real-world combat footage—spanning everything from electronic warfare interference to the movements of camouflaged ‘turtle tanks’—bridging the ‘sim-to-real’ gap that often causes sophisticated Western drones to fail in unpredictable, messy environments.
‘Software-defined’ battlefield
This data-centric approach has led to a ‘software-defined’ battlefield where the loop between a lesson learned, and a technical update is measured in days. Ukraine is now moving toward a procurement model where AI-driven analytics, rather than manual requests, determine which systems are purchased based on their real-world effectiveness. By treating every drone sortie as a data point in a broader matrix, the Ukrainian military is effectively closing the loop on procurement and employment, ensuring that only the most effective, attrition-tolerant technologies reach the front. This institutionalisation of failure analysis into the next generation of software means that the ‘Made in Ukraine’ badge has become a global gold standard for battle-proven, autonomous technology.
Ultimately, the implications of this laboratory stretch far beyond the current conflict. As human judgment gradually gives way to computer algorithms for target detection and navigation, the war’s most valuable legacy may be the creation of the world’s first ‘algorithmic’ military. The transition from industrial mass to algorithmic precision suggests that the countries that prevail in the future will not be those with the largest stockpiles of stagnant hardware, but those that can own and manage the ‘data polygons’ necessary to refine their autonomous systems in near-real time. Ukraine is no longer just fighting a war; it is hosting the debut of a future where data is the ultimate force multiplier.
The inversion of war economics signifies a fundamental shift where industrial capacity and software integration have eclipsed the traditional pursuit of ‘technological exquisiteness’ as the primary metrics of military power. For decades, the measure of a superpower was its ability to field a small number of nearly invulnerable, multi-million-dollar platforms. However, in the modern landscape, these ‘exquisite’ systems are increasingly vulnerable to ‘precise mass’—vast swarms of low-cost, autonomous drones that can be produced at a rate of thousands per day. This transition means that the ‘physical platform’ is becoming a commodity, while the true competitive advantage lies in the ‘compute foundation’ and ‘software-defined’ capabilities that allow these systems to be networked and updated in real-time. Consequently, the victor in future conflicts will not necessarily be the nation with the most expensive fighter jet, but the one that can maintain a resilient, high-volume industrial base capable of sustaining an ‘attrition-tolerant’ force that evolves faster than an adversary can target it.
Double-edged sword for smaller nations
For smaller nations like Sri Lanka, the arrival of this new military era offers a double-edged sword of strategic opportunity and profound vulnerability. Traditionally, small states were sidelined in the global arms race due to the prohibitive costs of ‘exquisite’ platforms like advanced fighter jets or missile destroyers, which often consumed unsustainable portions of a national budget. However, the shift toward ‘precise mass’ means that countries with limited resources can now develop significant deterrent capabilities through the localised production of low-cost, high-impact autonomous systems. By investing in software-defined defences and domestic drone manufacturing, a nation like Sri Lanka can achieve a level of coastal and territorial security that previously required a superpower’s investment. Not only that, but Sri Lanka can also develop into an export market for the new precise technology which has a wide demand from warring countries. Conversely, the democratisation of these ‘one-way’ technologies also means that non-state actors or regional adversaries can more easily threaten national infrastructure, forcing small nations to prioritise digital resilience and rapid technological adaptation over the maintenance of ageing, high-cost legacy hardware.
by Prof. M. W. Amarasiri de Silva
Features
Turning science into action: Prof. Gothamie Weerakoon calls out Biodiversity “Narratives”

By Ifham Nizam
In an exclusive interview with The Island, Ifham Nizam speaks with Professor Gothamie Weerakoon—Senior Curator and leading researcher on lichens and slime moulds at the Natural History Museum—who offers a candid, evidence-driven critique of corporate sustainability, global biodiversity governance, and the realities facing countries like Sri Lanka.
With over 450,000 specimens under her care and more than 100 new lichen species described through fieldwork across South and Southeast Asia, Prof. Weerakoon brings a rare combination of deep scientific expertise and frontline ecological observation.
Her message is clear: biodiversity loss is accelerating, and much of what is presented as “progress” remains largely unproven.
Excepts of the full interview
Q: The Natural History Museum speaks of turning science into action—what evidence is there that businesses are actually changing behaviour rather than rebranding sustainability narratives?
A:There is emerging evidence of change, but when biodiversity is the focus, the gap between action and narrative becomes much more visible.
Some companies are moving beyond broad commitments by measuring their impacts on ecosystems, setting targets to halt biodiversity loss, and reporting through frameworks like TNFD (Taskforce on Nature-related Financial Disclosures). But these are still the exceptions.
Real change becomes evident when businesses transform supply chains—eliminating deforestation-linked commodities, adopting regenerative agriculture, and working with local communities to restore ecosystems. Investment in habitat restoration and science-led, location-specific action also signals progress.
However, without clear baselines, measurable outcomes, and long-term commitment, biodiversity claims risk remaining abstract. At present, biodiversity is still more visible in corporate language than in verified outcomes.
Q: Are multinational corporations genuinely reducing their biodiversity footprint, or simply shifting environmental costs to developing countries like Sri Lanka?
A: The reality is mixed, but there is strong evidence that impacts are often being shifted rather than reduced.
Consumption in wealthier economies continues to drive habitat loss in biodiversity-rich regions. In countries like Sri Lanka, export-driven sectors, such as agriculture and rubber, contribute to deforestation and habitat fragmentation.
Companies may improve their environmental performance, domestically, while outsourcing ecological damage to regions with weaker regulation. So while awareness is increasing, most corporations are not yet reducing their global biodiversity footprint.
Q:How do you distinguish between credible biodiversity action and corporate greenwashing in real terms?
A:Credible action is science-based, measurable, and location-specific.
Companies must establish baselines, quantify their ecological impacts, and demonstrate real outcomes—such as reduced deforestation or restored habitats—verified independently.
Greenwashing, on the other hand, relies on vague terms like “nature-positive” without evidence. It often highlights small projects while ignoring major impacts, or depends on offsets instead of reducing harm.

Red Christmas lichens are not a species found in Arctic habitats. Instead, it is characteristic of tropical and subtropical regions, indeed found in the Sinharaja Forest Reserve, particularly in the Morningside and Pitadeniya areas
The key test is simple: can a company prove that biodiversity loss linked to its operations is declining in specific places over time? If not, it is likely narrative rather than action.
Q:Many biodiversity commitments remain voluntary—should there be legally binding global standards for corporate accountability?
A:Yes, there is a strong case for binding standards.
Voluntary commitments lead to uneven progress and make it difficult to separate genuine action from superficial claims. Legal frameworks could ensure consistent reporting, accountability, and minimum standards.
However, biodiversity is highly local. Any global system must allow for flexibility and support developing countries rather than imposing rigid rules.
Q:What sectors are currently causing the most irreversible biodiversity damage, and why are they still operating with limited restrictions?
A:The most damaging sectors include agriculture, forestry, mining, and fossil fuel extraction.
Agriculture—especially large-scale monocultures—drives deforestation and habitat loss. Mining and fossil fuels cause long-term ecological disruption, while marine ecosystems suffer from overfishing.
These sectors persist with limited restrictions because they are economically powerful, biodiversity loss is harder to quantify than carbon emissions, and global supply chains allow impacts to be outsourced. Regulation also remains fragmented and weakly enforced.
Q:In countries like Sri Lanka, development projects often override environmental concerns—how can science-based tools realistically influence political decision-making?
A:Science-based tools can make biodiversity loss visible and measurable.
Environmental impact assessments, ecological mapping, and predictive models allow policymakers to understand trade-offs clearly. When ecological risks are quantified, they become harder to ignore.
The key is integrating these tools into planning systems so environmental considerations are not optional, but a core part of decision-making.
- Phyllopsora species in Monatne forest of Sri Lanka
- Green Algal lichens are dominant in wet mountains in Sri Lanka
Q:Can biodiversity conservation truly coexist with large-scale infrastructure and energy projects?
A:Yes—but only if biodiversity is considered from the beginning.
Projects must be designed using science-based planning, avoiding sensitive ecosystems and incorporating mitigation strategies like wildlife corridors and habitat restoration.
Conservation and development are not inherently incompatible, but poor planning creates conflict.
Q:Are global biodiversity frameworks failing to address ground realities in developing economies?
They often fall short in implementation.
A:Global frameworks provide guidance, but must be adapted to local conditions. Developing countries face capacity constraints and competing priorities.
Success depends on building local scientific capacity, aligning goals with economic realities, and ensuring flexibility in how targets are applied.
 Q:What role should governments play when businesses resist biodiversity regulations citing economic pressures?
Q:What role should governments play when businesses resist biodiversity regulations citing economic pressures?
A:Governments must act as regulators and enforcers.
They should establish clear legal standards, backed by monitoring and penalties. At the same time, incentives—such as green finance and technical support—can help businesses transition.
Economic arguments should not override ecological realities, especially when long-term costs of biodiversity loss are considered.
Q:Are financial institutions doing enough to penalise environmentally destructive investments?
A:Not yet. While awareness of biodiversity risk is increasing, short-term profits still dominate decision-making. ESG frameworks exist, but enforcement is weak.
Stronger systems are needed—binding criteria, independent audits, and better integration of ecological risk into financial decisions.
Q:How can local communities be given real decision-making power rather than token consultation?
A:Communities must be recognised as partners, not stakeholders.
Legal rights, participatory planning, and co-management systems are essential. Traditional knowledge should be integrated with scientific data.
Without real authority, consultation becomes symbolic rather than meaningful.
Q:What immediate, science-backed interventions can be implemented in Sri Lanka?
A:Practical steps include restoring mangroves, creating wildlife corridors, and community-led reforestation.
Using GIS mapping and monitoring systems can identify high-risk areas, while sustainable livelihood programmes reduce pressure on ecosystems.
These interventions must be evidence-based and locally adapted.
Q:How can policymakers protect biodiversity-rich regions from short-term exploitation?
A:Through zoning laws, protected areas, and mandatory environmental assessments.
Valuing ecosystem services in economic planning is also critical. When biodiversity is treated as an economic asset, it becomes harder to ignore.
Q:What mechanisms exist to hold corporations accountable when biodiversity damage crosses borders?
A:International agreements, supply chain regulations, and reporting frameworks like TNFD play a role.
Financial institutions, legal systems, and civil society also contribute to accountability. But enforcement across borders remains a major challenge.
Q:Is there sufficient transparency in corporate biodiversity reporting?
A:No—current systems are inconsistent and largely voluntary.
Many companies fail to quantify their impacts, and independent verification is limited. Without standardised metrics and audits, transparency remains inadequate.
Q:How can biodiversity be integrated into national economic planning without slowing growth?
A:By recognising that biodiversity supports economic resilience.
Nature-based solutions—such as mangrove restoration or sustainable agriculture—deliver both ecological and economic benefits.
Strategic planning can align conservation with development rather than treating them as opposing goals.
Q:What are the long-term economic risks of biodiversity loss in South Asia?
A: They are severe. Declining pollination, soil degradation, and fisheries collapse threaten food security. Loss of forests and wetlands increases disaster risks.
Ultimately, biodiversity loss undermines economic stability and increases vulnerability to climate shocks.
Q:How can science communication better influence public opinion and policy?
A: By making data accessible and relevant.
Visual tools, storytelling, and collaboration with media can translate complex science into actionable insights. Public engagement is essential for policy change.
Q:Are current conservation models too dependent on international funding?
A:Yes, and that creates vulnerability.
Long-term sustainability requires diversified funding—government support, private investment, and community-based initiatives.
Local ownership is key to lasting impact.
Q:Ultimately, who should bear the greatest responsibility for reversing biodiversity loss?
A:Responsibility is shared—but governments hold the greatest leverage.
They set the rules, enforce regulations, and shape economic systems. Corporations and consumers also play critical roles, but without strong governance, progress will remain limited.
Prof. Weerakoon’s assessment is both measured and uncompromising: biodiversity loss is no longer a distant ecological issue—it is an economic, political, and social crisis.
Aligned with the mission of the Natural History Museum, her message is clear: the future of conservation depends not on promises, but on verifiable, science-based action grounded in real ecosystems—not narratives.
Features
Looming shadow: How and why a distant war could threaten vitality of Sri Lankan healthcare

An Independent Freelance Correspondent
As the sun sets over the Indian Ocean, the tranquil beauty of Sri Lanka feels many a world away from the smoke, thunder, misery and deaths in the Middle East, taking place in the midst of a senseless war. Yet for all that, in our interconnected world, a butterfly might flit its wings in the Gulf, and a storm might eventually break over our own little paradise island, as a strange reversal of the status quo. However, the escalating conflict in the Middle East is no longer just a distant headline for Sri Lankans; it is an ominous cloud gathering that threatens the very backbone of our much-bandied social contract, our healthcare system.
While we often view war through the lens of geopolitics or rising oil prices, the “Ground Zero” of its impact in Sri Lanka may well be the hospital ward, the local dispensary, and the dinner tables of our most vulnerable citizens, just as much as it would impact on the healthcare professionals who are responsible for maintaining a well-oiled machine; the pun being intentional.
The Fuel Paradox: When Mobility Becomes a Luxury
Our health service runs on wheels as much as it does on training and wisdom. The entire system has to be supported by energy. The Middle East remains the lifeblood of our energy supply, and any disruption to the Strait of Hormuz would send immediate shockwaves to our fuel pumps. Lack of fuel, as well as skyrocketing prices of oil, would have a cascading detrimental effect on our health service.
For the average citizen, a spike in fuel prices is not just a “transport issue” but a miserable calamity that could become a noteworthy barrier to life-saving healthcare. When bus fares double and three-wheeler charges skyrocket, a mother in a rural village may think twice and even hesitate to take her feverish child to the nearest Base Hospital. In the calculus of poverty, the cost of the journey often outweighs the urgency of the ailment, until and most unfortunately, it sadly and tragically becomes too late.
Furthermore, our healthcare workers, the doctors, nurses, public health midwives, clerks, orderlies, and other grades of minor staff, are certainly not immune to the impacts of the fuel crisis. Unlike many top-tier officials of the rest of the public service, most medical staff rely on their own vehicles or public transport to reach their posts. If fuel becomes a rationed luxury, we risk a kind of inevitable “silent strike” where the healers simply cannot afford to commute to the hallowed places of healing. The other grades of staff mentioned are certainly no less important to run the machine, and they will also be at the receiving end of the fuel crisis and transport problems.
A Bitter Pill: The Private Sector Squeeze
While the state provides free healthcare, the private sector has long acted as a vital pressure valve for the national system. However, the conflict is rapidly tightening the screws here as well.
=The Price of Healing: Most of our medicines and vaccines are imported. With global shipping routes disrupted and “war risk” insurance premiums surging, the landed cost of a simple strip of a commonly used medicine or a vital course of antibiotics to clear a lung infection would climb disproportionately.
=The “In-Patient” Inflation: Private hospitals are energy-intensive hubs. From the electricity that powers life-support machines to the diesel that runs emergency generators, rising costs will most unfortunately have to be passed directly to the patient.
=Consultation Charges: As overheads, maintenance costs, staff salaries, and medical supplies spiral, even the renowned Private Hospitals, as well as even the most dedicated private practitioners, would find themselves forced to increase fees.
When the private sector becomes unaffordable, those patients migrate back to the already overstretched state hospitals, creating a “domino effect” of long queues and exhausted resources.
The Empty Plate: Nutrition as the First Line of Defence will be in danger
Perhaps, the most insidious impact of the Middle Eastern crisis is the one that happens at the grocery store leading to great difficulties in getting food into the table. Sri Lanka relies heavily on remittances from our workers in the Gulf and the robust export of our “black gold”- Ceylon Tea. The war has stalled tea exports to major markets like Iran and Iraq, costing the industry millions every week. Simultaneously, if our workers in the Middle East face displacement, the flow of foreign exchange into our country, which would benefit even the villagers, might just dry up.
When a family’s income drops, the first thing to be sacrificed is often the “quality” and even the quantity of the food that comes onto the table. We might see a return to starch-heavy, protein-poor diets. For a pregnant mother, this means anaemia and untold risks to the yet-to-be-born baby. For a growing young child, it means stunting and weakened immunity. For the elderly, it will mean increasing the frailty of old age. We are essentially “importing” a future health crisis of malnutrition that no amount of free medicine can easily fix.
The Supply Chain Shadow
Modern medicine is a “just-in-time” industry. Many of our specialised vaccines and a variegated plethora of treatments require a “cold chain” – a continuous refrigerated journey. With major Gulf air hubs facing disruptions, these temperature-sensitive medicines must be rerouted. This adds days to the journey and increases the risk of “spoilage.” A vaccine that loses its potency due to a shipping delay is not just a financial loss; it is a lost shield for a child and even, older and elderly people.
Sadly, just like the fuel situation, there have not been any worthwhile efforts to “stockpile” at least some of the essential medicines. Of course, unlike just storing fuel to stockpile, medicines have their own problems with shelf-life and expiry dates. It is indeed a vexing problem that might cause a major, tricky situation at some time in the future. The government is planning to issue medicines for two months from the clinics etc. One only hopes that the currently available stock could be used effectively without that initiative leading to a desperate shortage of essential drugs.
Navigating the Storm: Some Ways to Mitigate the Crisis
This author has brought to light some of the issues that we may see in the future. However, it is not an exhaustive or complete list of all possible consequences. There could be quite a few more. While the situation is grave at present, it is perhaps not unmanageable. To protect the vitality of our healthcare, we must adopt a “War Footing” of preparedness:
1. Fuel Priority for Healthcare: The government must establish a “Green Lane” for healthcare personnel and emergency vehicles, ensuring that they have subsidised or prioritised access to fuel to prevent service interruptions. This has to include the private healthcare personnel as well.
2. Strategic Buffer Stocks: We must move away from “just-in-time” imports and build a minimum 6-month buffer stock of essential medicines and vaccines. We need to utilise regional cooperation with neighbours like India to diversify supply routes.
3. Strengthening Primary Care: By investing in local dispensaries and public health midwives, we can treat ailments before they require expensive hospital stays, as well as extended forms of treatment, reducing the transport burden on patients.
4. Nutritional Safety Nets: Expanding school meal programmes and providing fortified food supplements to pregnant mothers can act as a firewall against the malnutrition that is likely to be caused by economic shocks.
5. Digital Health Integration: Expanding “telemedicine” can allow specialists to consult with rural patients remotely, saving both the doctor and the patient the high cost of travel.
A Call for Preparedness, but not a Harbinger of Panic
It is ever so easy to read these points and see a looming, tremendously gloomy fog that could envelop our revered Motherland in the not-too-distant future. However, from a clearer perspective, the purpose of this analysis is not for the writer to act as a prophet of doom, but for this enterprise to serve as a wake-up call for proactive management and to take all necessary steps, well in time, to avoid a catastrophe.
Our health service is the crown jewel of our nation. It has been built on the Herculean effort of generations who believed that health is definitely a right, and certainly not a privilege. To protect it, we must look beyond our borders and understand that the proverb “a stitch in time saves nine” is what we need now. We must strengthen our social safety nets before the ripples of the Middle Eastern war become a tidal wave that hits our shores. We need to act purposefully now, to be able to steadfastly cushion whatever blows that might come our way in the future.
This is not a forecast of a disaster that is one-hundred per cent certain to occur. In stark contrast, it is meant to be a sober and sombre analysis of possible ramifications that we must prepare for today, to save the lives of our people and look after their health tomorrow.
Dr B. J. C. Perera
MBBS(Cey), DCH(Cey), DCH(Eng), MD(Paediatrics), MRCP(UK), FRCP(Edin),
FRCP(Lond), FRCPCH(UK), FSLCPaed, FCCP, Hony. FRCPCH(UK), Hony. FCGP(SL)
Specialist Consultant Paediatrician and Honorary Senior Fellow, Postgraduate Institute of Medicine, University of Colombo, Sri Lanka.
-

 News6 days ago
News6 days agoSenior citizens above 70 years to receive March allowances on Thursday (26)
-

 Features3 days ago
Features3 days agoA World Order in Crisis: War, Power, and Resistance
-

 News4 days ago
News4 days agoEnergy Minister indicted on corruption charges ahead of no-faith motion against him
-

 News5 days ago
News5 days agoUS dodges question on AKD’s claim SL denied permission for military aircraft to land
-

 Business5 days ago
Business5 days agoDialog Unveils Dialog Play Mini with Netflix and Apple TV
-

 Sports4 days ago
Sports4 days agoSLC to hold EGM in April
-
 News6 days ago
News6 days agoCEB Engineers warn public to be prepared for power cuts after New Year
-

 Business7 days ago
Business7 days agoPostponement of Sri Lanka Investment Forum 2026


















